Articles
Security
Securing Global Supply Chains
With trading partners spread across various regions, unique security risks associated with different countries, and an array of legal and regulatory regimes, global shippers must be well-prepared to ensure cargo safety. Bill Anderson, group director of security and international safety, Ryder System Inc., provides these tips for securing your international supply chain. 1. Create a […]
Read MoreManeuvering Freight Through Challenging International Areas
Do your 2011 business plans include shipping to areas where civil unrest or natural disasters have occurred? If so, be flexible and make strong connections, advises Larry Wenrich, vice president, government sales for Lima, Pa.-based Pilot Freight Services. Here are his tips on shipping to and from difficult areas. 1. Locate an airport with customs […]
Read More
Technology Powers New Supply Chain Security Systems
In a speech at the Massachusetts Institute for Technology in March 2011, Department of Homeland Security (DHS) Secretary Janet Napolitano said, “Innovation is critical to economic growth, international competitiveness, and national security. We must expand government’s collaboration with the science and engineering communities in industry and academia to include a deeper, broader partnership on homeland […]
Read More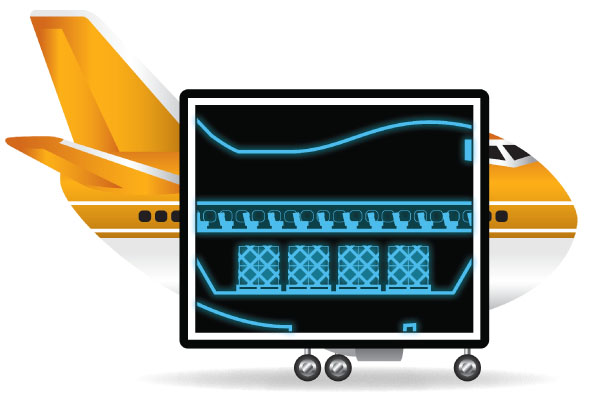
Trends—May 2011
100% Screening Deadline Up in the Air The air cargo industry, manufacturers, exporters, importers, and consumers face the prospect of dramatic global supply chain disruption if the U.S. Transportation Security Administration (TSA) enforces a proposed deadline of Dec. 31, 2011, for 100-percent screening of all international inbound cargo on passenger aircraft. The subject dominated The […]
Read More
Container Security: Filling in the Blanks
It is often impossible to know what containers entering the United States really contain. Even with bonded shipments and the 24-hour manifest required by U.S. Customs and Border Protection’s Container Security Initiative, we merely take the shipper’s word as to a container’s contents, never knowing whether its security has been compromised during transit. Using Container […]
Read MoreShipping Cross-Border and Within Mexico
Troy Ryley and Jose Minarro, managing directors for Transplace Mexico, offer tips for shipping freight cross-border and within Mexico.
Read More
Securing the Supply Chain
Smart shippers take the necessary steps to protect their products, shipments, and logistics operations.
Read MoreGlobal Logistics – December 2010
China Full of Beans China’s consuming population continues to expand without pause, as demand for American Joe is now competing with a long-standing cultural mainstay —green tea. Starbucks has inked a deal with the Chinese provincial government of Yunnan to set up its first coffee bean farm. The Seattle chain is partnering with local growers […]
Read MoreTrends—December 2010
A Cellular Distraction Exposes DOT’s Blind Spot When U.S. Transportation Secretary Ray LaHood recently took one hand off the Department of Transportation (DOT) steering wheel long enough to field another call about the dangers of cell phone use while driving, freight industry outsiders were eavesdropping. Truth be told, they’d prefer riding shotgun, even at their […]
Read MoreA Supply Chain PIP Squeak
At the risk of launching yet another industry acronym, efficient supply chains require PIP: people, intelligence, and good processes.
Read MoreBalancing Risk Management With Your Operations Strategy
As the nation’s economy recovers from the recent downturn, the domestic freight industry represents a leading indicator of commercial activity and (hopefully) corporate profits. Asset-based carriers, a segment that has taken it on the chin the past few years, are thought to have pricing power because increasing freight volumes—albeit off severe lows—have been met with […]
Read More
Ties That Bind: Sewing Up U.S.-Canada Trade
A steady stream of goods passing north and south across the U.S.-Canada border stitches the two nations tightly together, complicated by factors such as customs regulations, security protocols, data exchange, and infrastructure projects.
Read More
Digitizing the Global Supply Chain
At one point, we all had a rabbit-eared TV or a clunky cell phone that took muscle to carry. Numerous electronics innovations have made life not only easier, but also more productive. So why are so many international supply chain professionals still living in the dark ages when it comes to supply chain efficiency and […]
Read More
Gearing Up for 100% Air Cargo Screening
A complex shift in the air cargo industry begins in August 2010, when the Transportation Security Administration (TSA) will require 100-percent screening of all air cargo carried in passenger planes departing from or arriving at U.S. airports. In response to the Sept. 11 terrorist attacks, the TSA created a security mandate with an initial step […]
Read MoreThe Full Cost of Cargo Losses
All too often, supply chain managers do not properly calculate all the elements of cargo loss. As a result, they minimize the full impact on their bottom line. Most look only at cargo theft or damage to determine the financial impact on their company. Many other factors, however, need to be considered when calculating the […]
Read MoreCross-Border Stewardship
A new cross-border compliance initiative helps smaller shippers become more proficient supply chain partners.
Read MoreTightening Supply Chain Security
Theft, terrorist activities, or cargo loss can happen on ocean vessels, at ports, in airports, at loading docks, or in transit. Don’t leave your inventory and equipment vulnerable. Here are 10 tips for tightening security along your supply chain, from Chris Corrado, vice president customer support, APL Logistics. 1. Participate in the Customs-Trade Partnership Against […]
Read MoreMaritime Security: Creating a System of Systems
Nearly every containerload represents a point of vulnerability in the pursuit of maritime security. Daily, 17,000 shipping containers laden with cargo of all sorts enter 361 U.S. seaports. Multiply this number by the hundreds of pairs of human hands through which that cargo passes and you can begin to see the magnitude of the port […]
Read MoreSeeing’ Safe Ports: Connect to Protect
The emergence of new global logistics challenges in the wake of Sept. 11 has prompted the U.S. government to effectively secure our borders. But, of the 5.7 million containers arriving in the United States each year, less than two percent of all shipments offloaded at U.S. ports are inspected prior to arrival. Limited human resources […]
Read MoreTruckers Unite to Combat Terrorism
Last September, our nation and the trucking industry were shaken by the realization of our vulnerability to terrorist attacks. While the trucking industry has fought to combat cargo theft and address other security concerns for many years, never before have we considered the magnitude of tragedy that can occur when cargo and equipment fall into […]
Read More