Articles
Security
Great Expectations
Even amid economic uncertainty, shoppers expect global businesses to maintain fast and transparent delivery, improve environmental sustainability, and keep personal data secure, according to new research from project44. Key findings from the report highlight: Fast Deliveries 83% of consumers do not expect companies to give up fast delivery in an economic downturn. 89% do not […]
Read More
Three Ways to Mitigate Insider Risk in Your Supply Chain
“Insider threat” has long been a familiar security topic for C-suite executives in every industry. In fact, 90% of organizations feel vulnerable to insider attacks, according to IBM. Yet, when creating risk mitigation programs for insider threats, many organizations overlook their nonemployees—the people who work for their third-party vendors, partners, and contractors.
Read More
What’s Lurking in Your Supply Chain?
You may think your company is well protected when it comes to cybersecurity, but an often overlooked source of vulnerability is your supply chain. If you can’t honestly say you are fully apprised of the security postures of your vendors, partners, and contractors, then you are already at major risk of a cyberattack.
Read More
3 Big Barriers to IIoT Integration
From monitoring air quality in "smart cities" like Chicago and New York City to tracking health data in real time on smart watches, the Internet of Things (IoT) is everywhere. IoT applications look promising for the manufacturing industry as well: European aircraft manufacturer Airbus is developing Industrial Internet of Things (IIoT) technologies to provide valuable […]
Read More
Stop, Thief! Five Ways to Protect Your Supply Chain
Today’s supply chain ecosystem is increasingly complicated. We rely on suppliers and buyers across the globe and use multiple transport modes, languages, currencies, and laws across borders.
Read MoreGoing the Distance: Securing Supply Chains From Cyber Attack
All over the world, business are achieving their goals with more ease than ever before, thanks to digital disruption. Ambitions that would have taken decades to achieve in the past can now be attained in significantly less time, whether you are expanding globally, automating low-level tasks or scaling up. But this digital awakening has also […]
Read More
Eight Ways to Minimize Supply Chain Risk
Supply chain attacks aren’t anything new, but threat actors continue to find new ways to breach networks. The 2013 Target breach and more recent NotPetya, Trisis, and Wipro compromises serve as not-so-gentle reminders that supply chain attacks are damaging and costly and present many risks to both businesses and their suppliers.
Read More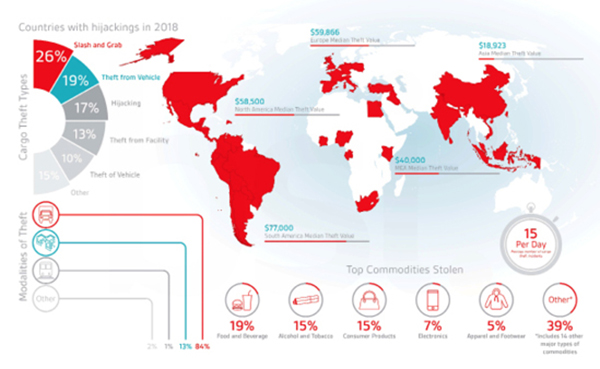
Stop, Thief!
TT Club and BSI have issued the second edition of their report on global cargo theft, the first to cover a full year. The report analyzes cargo theft by modality, theft type (modus operandi), commodities targeted, and the value of losses across the major regions of the world (see chart above). Among the notable findings: […]
Read More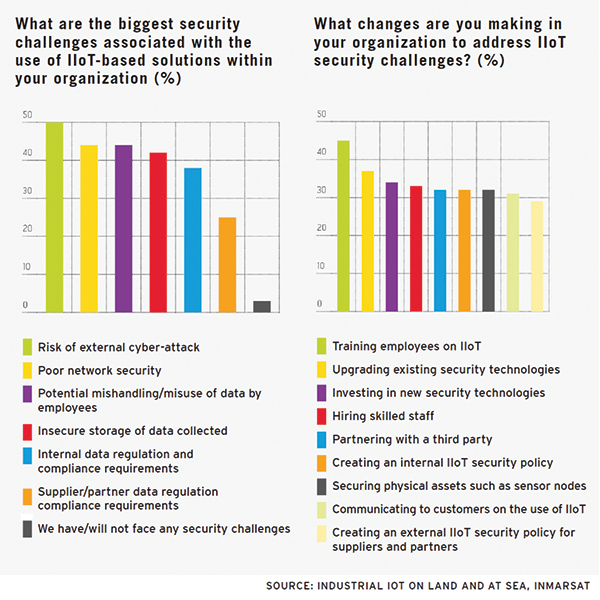
Is Your IoT Deployment Secure?
Transportation and logistics companies recognize they must strengthen their approaches to cybersecurity but are not yet taking the practical steps to safeguard their industrial Internet of Things (IoT) deployments, according to a study done on behalf of Inmarsat. According to the study, which surveyed 125 businesses across the transport industry, 64% of respondents say their […]
Read More
The ABCs of Supply Chain Cybersecurity
Supply chain cybersecurity is one of the biggest issues facing logistics planners.
Read MoreDefending Against Supply Chain Hackers
While your company may have excellent cyber security practices in place, your suppliers may not. These best practices will help protect your company from hackers who attack your supply chain partners. 1. Review Incident Response Plans. Always make sure vendors have an incident response plan in place before conducting business with them. If there is […]
Read MoreGuarding Your Business Against Data Loss
Data loss is every company’s nightmare. In fact, most companies that do experience a mass disappearance of vital, computer-kept information never turn their lights on again. It comes down to the idea that how you protect and treat your data is commensurate with how important you think it is, says Penny Garbus, co-founder of Soaring […]
Read More
10 Ways To Play IT Safe
State-sponsored and individual bad actors will escalate supply chain cybersecurity risks. Here are 10 threats and trends to look out for across business, governmental, and personal arenas: 1. Software updates—the new Trojan Horse. Criminals use the normal software update process to get companies to infect all their clients, which then affects everyone down their software […]
Read More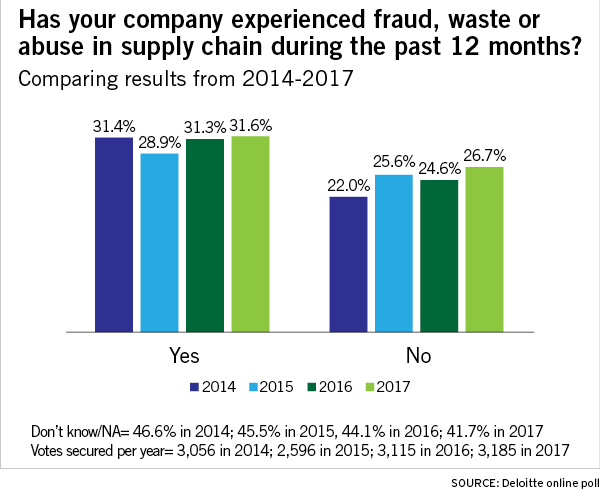
Fraud Goes Broad
The use of analytics to mitigate third-party supply chain fraud, waste, and abuse risk jumped to 35 percent in 2017 from 25.2 percent in 2014,according to a Deloitte poll. Between 2014 and 2017, an average of 30.8 percent of poll respondents report at least one instance of supply chain fraud, waste, and abuse in the […]
Read More
Cargo Security: The Art of the Steal
Keeping your cargo safe from theft is a bigger challenge than you might think. Follow these steps to reduce the risks that make your company a target.
Read More
IBM: Working on the Blockchain Gang
Security. Transparency. Efficiency. These buzzwords have circled the supply chain for years as consumers demand more responsible supply chains, forcing shippers and providers to explore new ways to make these terms reality. Alongside these buzzwords, another word surfaces as a potential solution to many major concerns: blockchain. IBM aims to make this solution tangible for […]
Read More
Is Ransomware Holding Global Trade Hostage? Here’s How to Safeguard Your Supply Chain
In June 2017, another major cyberattack targeted several large multinational corporations. The malware Petya (or NotPetya or Nyetya) was able to breach dozens of Russian and Ukrainian companies, including Russian oil and gas giant Rosneft, as well as leading global businesses across multiple industries. This time, two giants in the logistics industry, Maersk and FedEx, […]
Read MoreSupply Chain Security: Defending Against a Data Breach
What a wonderful world this would be if protection from cybersecurity threats were contained within the four walls of your business. But the hard truth is every entity on your company’s supply chain list – from the most active vendor account to the least – must be fully vetted to ensure they are protecting theirs […]
Read More
High Value, High Risk: How to Make Sure Your Cargo is Protected
If your company is shipping a load valued at $100,000 or more, you should take every step possible to make sure your cargo is protected. Here are five ways you can greatly lower the risk of losing hundreds of thousands of dollars from a failed shipment. 1. Check your insurance coverage. First, you need to […]
Read More
Commentary: Supply Chain System Security Starts in the Cloud
The May 2017 ‘WannaCry’ ransomware cyberattack swept 150 countries, crippling hospitals, paralyzing government entities, and completely halting businesses by exploiting vulnerabilities in outdated operating systems. By infiltrating systems, locking down digital assets, and making all files and folders inaccessible, the attackers effectively shut down entire organizations. No fulfillment. No new client acquisition. No checking inventory. […]
Read More