Articles
Security
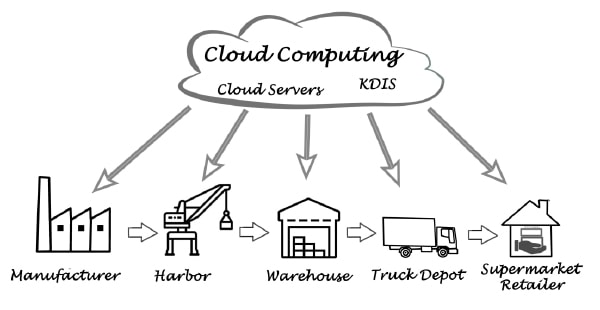
The Future of the Supply Chain is Cloudy
We hear a lot about the cloud these days. The cloud (public or private) refers to software and services that run on the Internet instead of locally on your computer. There is a good chance that the majority of business data will eventually reside in the cloud.
Read More
Keeping Your Digital Supply Chain Secure
Organizations that are most protected from cyberattacks are ones that understand what threats exist in the first place. This means having a good understanding of their entire supply chain as well as the data they are responsible for and where it is stored. 1. Understand the biggest threats to the digital supply chain, what data […]
Read More
Fighting Crime with AI
The pandemic has exacerbated the risks of these crimes in the past two years. There has been an explosion of new risks and challenges as fraudsters and traffickers have become increasingly skilled at falsifying documents, submitting false insurance claims, and finding funding to carry out crimes wherever they can. Organizations large and small are hard […]
Read More
Integrating NFC and Blockchain
Counterfeit supply chains cost U.S. manufacturers upwards of $131 million, and the problem is growing amid supply chain shortages. This crisis is also exacerbated by a time of technological advancement—not only are supply chains carrying in-demand products, but they also house incredible amounts of data that are susceptible to breach. Of the many security threats […]
Read More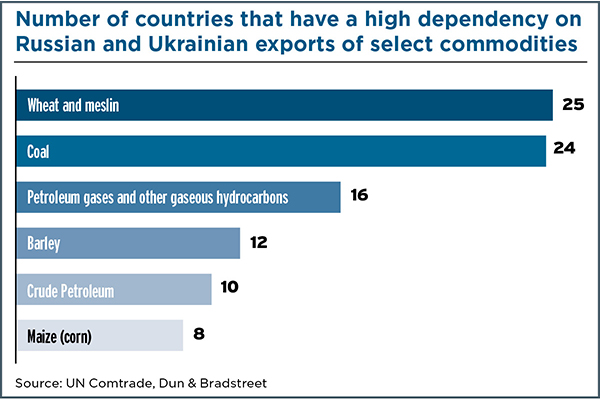
Russia-Ukraine Supply Chain Strain
The commodities markets are the industry category that is experiencing the greatest strain as a result of Russia’s invasion of Ukraine, according to a Dun & Bradstreet briefing report released in March 2022. The report, which assesses the global business impact of the crisis, focuses on the businesses and countries that work with Russian and […]
Read More
Cargo Security: Have a Safe Trip
From leveraging bottlenecks to launching malware attacks, criminals are targeting the supply chain. Here’s how to keep your freight—and information—safe.
Read More
National Security Starts With Individual Manufacturers
Shortages of personal protective equipment (PPE) and other critical supplies like pharmaceutical ingredients and materials used in key technologies during the earliest days of the pandemic prompted the Biden-Harris Administration in 2021 to outline steps strengthening critical supply chains. It’s a long-overdue move that to some transportation experts may not go far enough in protecting national security.
Read More
4 Steps to Building Cyber-Resiliency
Cyber-exploitation through contractor networks is becoming more prevalent. Cyber-insecure suppliers and contractors provide covert backdoor access to more prominent corporations.
Read More
Logistics Management & Chain of Custody: Securing IT Assets
Proper logistics management can be one of the most critical aspects of a successful IT asset disposition (ITAD) program.
Read More
Best Practices to Protect Supply Chains
With the rapid adoption of cloud computing and the Internet of Things (IoT), the supply chain has many new entry points and attack surfaces for cybercriminals to infiltrate. Implementing these best practices help manufacturers continue to innovate, create new products and services, and increase profitability, while maintaining a competitive edge.
Read More
Eastman Alert: What’s Your Emergency?
October 4, 2017 was a scary day at Eastman Chemical Company’s Kingsport, Tennessee, headquarters.
Read More
Chemical Logistics on a Roll
Overcoming capacity constraints, severe weather, and cyberattacks, chemical logistics service providers combine expertise and dedication to keep shipments moving safely and efficiently.
Read MorePRODUCT SPOTLIGHT | Cargo Security
GT 1210 Solution: ORBCOMM’s system combines asset tracking capabilities with cargo and door sensors. The trailer tracking device identifies door opens, route deviations, and loaded/unloaded status. Real-time alarms protect cargo from theft and tampering. The solution includes a customizable application with dashboards and analytics. IntelliScan Image Capture and Retrieval: Spireon’s cargo sensing technology complements its […]
Read More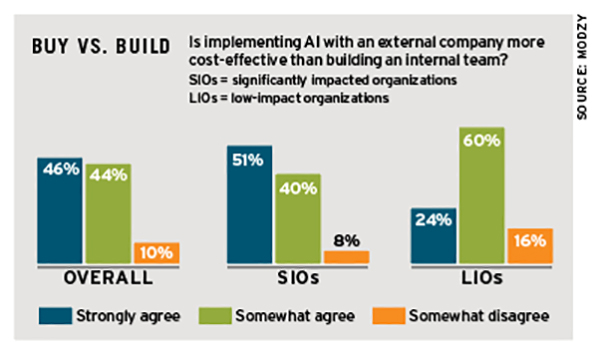
AI Strategy: Your Move
Artificial intelligence (AI) spending shows no signs of slowing, with 82% of decision-makers saying they’re very likely to increase their AI investment or capabilities in the next two years, says a report from Modzy. Decision-makers should consider the following factors in their AI strategy, the report says: Recognize the value. About 66% of decision-makers surveyed […]
Read More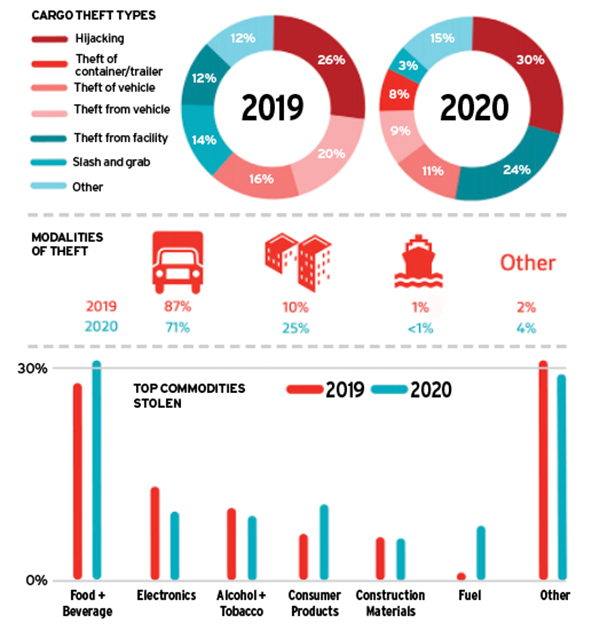
The Art of the Steal
With pandemic-induced lockdowns, e-commerce surges, and transportation restrictions in 2020, cargo theft shifted to new commodities and locations (see chart), says a BSI and TT Club report. New trends include the food and beverage sector experiencing the most theft, as well as an uptick in theft from facilities compared to 2019. In the year ahead, […]
Read More
Can Your Supply Chain Withstand the Unexpected?
Today’s supply chain is vast, expanding to every corner of the globe. With this expansion, the threat has increased significantly due to the larger attack surface. Add to that a global pandemic and the need to protect the supply chain has never been more important.
Read MoreYou’ve Got Drone Mail
Many drone delivery services involve dropping packages on the ground outside of homes and businesses, making them vulnerable to theft and bad weather. That’s where the smart drone mailbox comes in. These new mailbox concepts, developed by startups Valqari and DRONEDEK, involve a technology-enabled container that receives and stores packages in a secure, climate-controlled box […]
Read More
How Ransomware Kidnaps Supply Chains
The volume and sophistication of cyberattacks has increased in recent years, but even more so with COVID-19 and the shift to remote work. Most notably, there has been a particularly concerning rise in ransomware attacks.
Read MoreHow to Protect Your Supply Chain from Cyberattacks
Supply chains have been stretched to their limits by COVID-19 lockdowns, border closures, and sudden shifts in consumer demands. Now, they’re facing a growing threat from hackers. According to the FBI, cyberattacks have surged by 400% during the pandemic. One of the top targets: supply chains. In 2019, there were around 300 major hacks on […]
Read MoreIndustry Insight
In its 2020 survey covering companies’ priorities and challenges related to cybersecurity, advanced technologies, succession planning, and trade developments, technology company Sikich finds: 50% of manufacturing and distribution executives say they experienced a cyberattack in the past year, but most haven’t taken important cybersecurity prevention measures. 40% say they perform data breach prevention, such as […]
Read More