Risky Business: Inside the Freight Fraud Surge

Escalating cargo crime is forcing shippers and carriers to rethink risk, visibility, and security.
 Among the many challenges facing the supply chain today, few generate more buzz than freight fraud and cargo theft. And for good reason—this one-two punch is exacting a growing toll on logistics networks, emerging as one of the most significant risk factors for shippers, carriers, and brokers across the globe.
Among the many challenges facing the supply chain today, few generate more buzz than freight fraud and cargo theft. And for good reason—this one-two punch is exacting a growing toll on logistics networks, emerging as one of the most significant risk factors for shippers, carriers, and brokers across the globe.
From physical theft of freight in transit to increasingly sophisticated financial and identity scams, the threat landscape has expanded dramatically over the past several years. Experts say the problem isn’t stabilizing; it’s evolving.
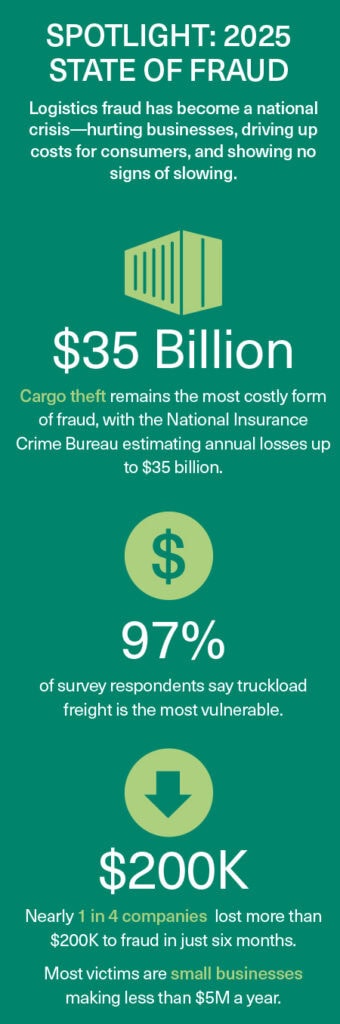
Recent industry research underscores the scale of the challenge. Since 2021, organized theft has increased by more than 1,500%, with estimated annual losses up to $35 billion, notes Chris Burroughs, president and CEO, Transportation Intermediaries Association (TIA).
TIA’s 2025 State of Fraud in the Industry report shows that truckload freight remains the top target of fraud, with an overwhelming 97% of respondents identifying it as the most fraud-prone mode (see graphic, right).
Nearly every participating company reported experiencing multiple types of fraud in a recent six-month period, and unlawful brokerage—where bad actors pose as legitimate brokers to steal loads or payments—was the most commonly cited scam. Spoofing, identity theft, phishing, fictitious pickups, and impersonation were also prevalent, showing that the fraud threat landscape remains varied and sophisticated.
Top Concern: The Bottom-Line Impact
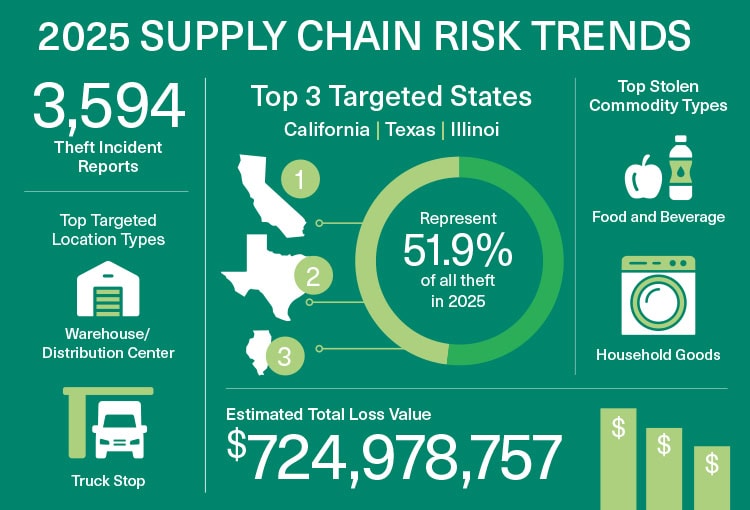
Estimated losses from supply chain crime incidents surged to nearly $725 million in 2025, a 60% increase from 2024, according to new data from Verisk CargoNet. The analysis also shows the average value per theft rose to $273,990, up 36% from $202,364 in 2024.
The implications far exceed isolated losses. Fraud and theft erode margins, disrupt operations, and threaten the reliability of partner networks.
“Every stolen load represents not merely a financial loss, but also a threat to a shipper’s reliability,” says Burroughs. “As shippers and their customers expect precision, transparency, and resilience, a stolen load can result in potentially irreparable damage to reputations, revenues, and jobs.”
“Fraud is no longer just about the freight—it’s about exploiting every weak link in the chain,” noted Kevin Clonch, Ryder’s group director, global transportation procurement, during a 2025 Inbound Logistics webinar, “Stop Freight Fraud Before it Starts: Proven Tactics for Vetting and Control,” which also featured carrier vetting platform Highway.
Data bears out Clonch’s sentiment. A recent index published by Highway finds that scammers attempted hundreds of thousands of sophisticated fraud attacks in the first quarter of 2025 alone. These attempts included compromised email accounts, caller ID spoofing, and unauthorized access attempts—all tactics aimed at gaining control of freight or carrier networks.
Shippers, freight brokers, and carriers report significant losses from this new wave of sophisticated crime: The 2025 TIA survey shows 22% of respondents lost more than $200,000 due to fraud in the past six months, and another 10% spent more than $200,000 on prevention efforts.
A New Wave of Criminal
“Criminal groups aren’t relying on chance anymore; they’re operating like disciplined enterprises. They study how freight moves, identify weak points in the process, and strike when visibility drops or communication slows,” explains Nolan Dragon, sales team lead at Tive.
These sophisticated bad actors can exploit even the slightest oversight, he notes: “They might swap a lowercase ‘i’ with an uppercase ‘I’ in a domain name to make a phishing email or BOL appear authentic.”
The challenge isn’t just preventing theft; it’s recognizing the early signals that indicate something is off, long before the truck moves. “Shippers and carriers must now turn to tools that authenticate identities, validate behavioral patterns, and flag anomalies,” Dragon says.
“Advances in technology have inadvertently empowered fraudsters,” adds Jenn Mead, founder and CEO of S-2international. “Fake insurance certificates, falsified authority documents, and other convincing forgeries make it increasingly difficult to distinguish legitimate companies from fraudulent ones. This heightens the need for careful vetting and due diligence at every stage.”
Despite the complexity of the threat, fighting back is not insurmountable. Effective fraud and theft mitigation is possible, through a mix of technology, process discipline, collaboration, and vigilance.
As a starting point, proper and thorough carrier vetting and strict financial controls are essential to deterring fraud. Technology platforms such as FreightValidate, Carrier 411, and Highway have become valuable tools for verifying critical data and identifying red flags.
Carrier vetting is not a one-time event, however. Dormant carriers that suddenly reactivate, mismatched VIN and insurance data, suspicious contact information changes, and offers that are “too good to be true” all warrant scrutiny, according to Clonch.
At Ryder, he explained, procedures are standardized and layered. “We lean heavily on technology to automate checks so our team can focus on strategic calls,” Clonch said. Phone communication is prioritized over email, and only verified contacts are engaged. Evaluating a carrier’s financial health is also part of the process, since distressed operators may be more vulnerable to fraudulent activity.
For Highway, combating fraud starts with authenticating and verifying motor carriers in ways similar to financial institutions. “The goal is to eliminate fraud by requiring carriers to prove who they are and what they can do—while also reducing friction for brokers and carriers,” explained Michael Caney, the platform’s chief commercial officer. Highway’s system automates routine checks with custom rules, freeing staff to focus on exceptions.
Beyond frontline vetting, Caney stressed the importance of back-office safeguards. These include sending rate confirmations only to trusted providers, avoiding load number exchanges unless initiated by staff, and auditing all payments against verified carriers and unaltered proofs of delivery.
Leveraging Technology for Detection
Technology also plays a key role in cargo theft and fraud deterrence. “As bad actors become more sophisticated and backed by substantial financial resources, shippers, third-party logistics providers, and brokers need to bolster their fraud prevention strategies with investment in advanced technology and systems to monitor and verify carrier legitimacy—both pre- and post-tender—including advanced verification processes, real-time tracking systems, and artificial intelligence to identify and flag suspicious activity,” says Andrew Wimer, senior director, operations and professional services, Descartes.
“The first step is to implement layered visibility,” adds Tive’s Dragon. “Criminal groups thrive by exploiting small blind spots in tracking, communication, and verification. Layered visibility closes those gaps by integrating real-time data, physical security signals, and continuous monitoring into one unified picture of a shipment’s behavior.”
By combining live tracking with constant monitoring, companies gain continuous awareness of a load’s location, movement patterns, door openings, route deviations, and stop durations. When these signals work together, any abnormal behavior triggers an immediate alert. “That early detection breaks the predictable patterns bad actors rely on and gives teams the chance to intervene before a theft occurs, instead of trying to retrace a missing shipment after the fact,” Dragon says.
Wimer advises a protection plan that includes enforcing two-factor authentication; using geolocation and image verification to validate carriers, vehicles, and drivers; and extending fraud monitoring into phone and email workflows to detect impersonation before transactions occur. He also recommends shippers strengthen pre-tender screening with deeper visibility into carrier history, assets, and compliance, while using post-tender performance data—such as tracking compliance and on-time delivery—to continuously refine carrier vetting and manage risk by exception.
From Reactive to Predictive
Not surprisingly, AI is also playing an important and emerging role in the new approach to combatting supply chain crime. “AI is helping fight fire with fire against the new breed of sophisticated, AI-generated fraud like indistinguishable phishing or vishing attempts,” explains Lou Amo, president, truck brokerage, RXO. “It shifts security from reactive to predictive, using ML to spot anomalies—like suspicious route deviations or fake credentials—before the load is lost.”
“Combined with blockchain-like technologies for identity verification and multi-sensor inputs (from drones or seismic sensors), AI will create an interoperable network that spots threats faster than humans can,” explains Milan Luketic, chief technology officer, Birdseye Security Solutions.
AI’s ability to learn may be its biggest advantage over more traditional technologies. With every load, AI-enabled solutions become better at recognizing the small, often imperceptible shifts that indicate impersonation, document manipulation, digital tampering, or coordinated theft.
“That pattern-based visibility is becoming essential as criminal networks use increasingly sophisticated tactics to blend in with legitimate operations,” explains Dragon.
On the flip side, Highway’s Caney advised businesses experimenting with AI to ensure they don’t inadvertently create new entry points for fraudsters. “Bad actors are innovative too. We need to stay a step ahead,” he cautioned.
Process, Culture and Collaboration Matter, Too
Yet, even the best tools and knowledge are not enough on their own. “Fostering integrity and security requires a balanced approach—combining technology, human expertise, and trust-based relationships,” notes Mead. “Building long-term, trusted relationships with carriers, logistics companies, and shippers creates the foundation for preventing fraud. Consistently working with reliable carriers allows businesses to develop a deeper understanding of their operations, making it easier to detect inconsistencies or suspicious activity.”
For Clonch, freight fraud requires a zero-trust mindset, where every interaction and entity is verified before trust is granted. He warned that the industry must work together and stay a step ahead of bad actors as they innovate new ways to exploit gaps.
“Without industry-wide commitment, the deterrents are just too weak,” Clonch noted.
On the commitment front, trade groups such as TIA are advocating for tougher regulatory oversight and improved enforcement of carrier registration and identity verification systems. The group has expanded its collaboration with the FBI to enhance information-sharing between the transportation industry and law enforcement and accelerate the reporting of incidents.
One part of the partnership is TIA’s enhanced Cargo Theft & Strategic Theft Hotline, which provides a way for brokers, 3PLs, and shippers to report suspicious activity. “Real-time reports will enable the FBI to recognize crime patterns more quickly and potentially identify connections between incidents that might otherwise appear unrelated,” Burroughs notes.
Looking Forward
As logistics networks continue to digitize and globalize, the complexity of fraud and theft risks will likely grow. Artificial intelligence and automation bring both promise and peril: While tools like predictive analytics and machine learning can boost fraud detection, the same technologies may also be leveraged by bad actors to launch more convincing scams.
For shippers and supply chain professionals, the imperative is clear: invest in layered defenses, cultivate vigilant cultures, and participate in broader industry efforts to share intelligence and strengthen guardrails.
Behind the Surge
Industry experts share their thoughts on what is driving the escalation of freight fraud and theft:
What’s Trending in 2026?
Cyber threats are growing more sophisticated and operationally disruptive, with AI-assisted social engineering, automated attack frameworks, and supply-chain compromise emerging as defining trends for the year ahead, according to the National Motor Freight Traffic Association’s 2026 Transportation Industry Cybersecurity Trends Report.
These dynamics illustrate a threat landscape that no longer affects only back-office systems, but also physical operations and cargo integrity.
The reports cautions supply chain professionals to prepare for the following:
- AI-augmented attack vectors that evade traditional defenses and accelerate compromise.
- Automated attack orchestration that outpaces manual detection and response.
- Weaponization of legitimate access tools and APIs, expanding threat entry points.
- Supply-chain trust exploitation through third-party software-as-a-service (SaaS) and integration dependencies.
- Regulatory shifts influencing operational accountability and compliance planning.
